A best online resource to prepare for the EC-COUNCIL 312-50V11 exam: the latest 312-50V11 practice test. The latest 312-50V11 exam dumps pdf. Pass4itsure full 312-50V11 dumps https://www.pass4itsure.com/312-50v11.html (Total Questions: 429 Q&A 312-50V11 Dumps Pdf) can help you pass your first exam!
New 2021 EC-COUNCIL 312-50V11 dumps pdf from google drive (Update Questions)
Welcome to download [free questions] EC-COUNCIL 312-50V11 dumps pdf https://drive.google.com/file/d/1xZM63lHp46CFESTKrsT8Spj-cJGxC42A/view?usp=sharing
New EC-COUNCIL 312-50V11 exam practice questions(q1-q13)
QUESTION 1
What hacking attack is challenge/response authentication used to prevent?
A. Replay attacks
B. Scanning attacks
C. Session hijacking attacks
D. Password cracking attacks
Correct Answer: A
QUESTION 2
Why would you consider sending an email to an address that you know does not exist within the company you are
performing a Penetration Test for?
A. To determine who is the holder of the root account
B. To perform a DoS
C. To create needless SPAM
D. To illicit a response back that will reveal information about email servers and how they treat undeliverable mail
E. To test for virus protection
Correct Answer: D
QUESTION 3
Nedved is an IT Security Manager of a bank in his country. One day. he found out that there is a security breach to his
company\\’s email server based on analysis of a suspicious connection from the email server to an unknown IP
Address.
What is the first thing that Nedved needs to do before contacting the incident response team?
A. Leave it as it Is and contact the incident response te3m right away
B. Block the connection to the suspicious IP Address from the firewall
C. Disconnect the email server from the network
D. Migrate the connection to the backup email server
Correct Answer: C
QUESTION 4
How does a denial-of-service attack work?
A. A hacker prevents a legitimate user (or group of users) from accessing a service
B. A hacker uses every character, word, or letter he or she can think of to defeat authentication
C. A hacker tries to decipher a password by using a system, which subsequently crashes the network
D. A hacker attempts to imitate a legitimate user by confusing a computer or even another person
Correct Answer: A
QUESTION 5
While scanning with Nmap, Patin found several hosts which have the IP ID of incremental sequences. He then decided
to conduct: nmap -Pn -p- -si kiosk.adobe.com www.riaa.com. kiosk.adobe.com is the host with incremental IP ID
sequence. What is the purpose of using “-si” with Nmap?
A. Conduct stealth scan
B. Conduct ICMP scan
C. Conduct IDLE scan
D. Conduct silent scan
Correct Answer: A
QUESTION 6
Every company needs a formal written document which spells out to employees precisely what they are allowed to use
the company\\’s systems for, what is prohibited, and what will happen to them if they break the rules. Two printed copies
of the policy should be given to every employee as soon as possible after they join the organization. The employee
should be asked to sign one copy, which should be safely filed by the company. No one should be allowed to use the
company\\’s computer systems until they have signed the policy in acceptance of its terms.
What is this document called?
A. Information Audit Policy (IAP)
B. Information Security Policy (ISP)
C. Penetration Testing Policy (PTP)
D. Company Compliance Policy (CCP)
Correct Answer: B
QUESTION 7
Peter extracts the SIDs list from Windows 2000 Server machine using the hacking tool “SIDExtractor”. Here is the
output of the SIDs: From the above list identify the user account with System Administrator privileges.
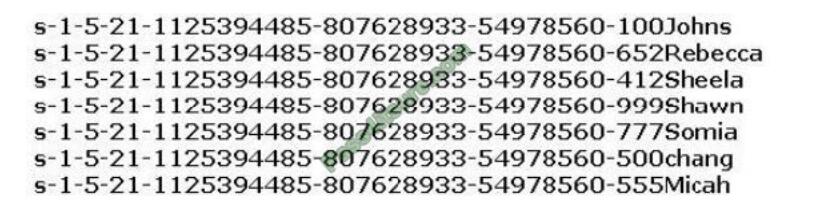
A. John
B. Rebecca
C. Sheela
D. Shawn
E. Somia
F. Chang
G. Micah
Correct Answer: F
QUESTION 8
An organization has automated the operation of critical infrastructure from a remote location. For this purpose, all the
industrial control systems are connected to the Internet. To empower the manufacturing process, ensure the reliability of
industrial networks, and reduce downtime and service disruption, the organization deckled to install an OT security tool
that further protects against security incidents such as cyber espionage, zero-day attacks, and malware. Which of the
following tools must the organization employ to protect its critical infrastructure?
A. Flowmon
B. Robotium
C. Balenadoud
D. intenlFuzzer
Correct Answer: A
QUESTION 9
A hacker is an intelligent individual with excellent computer skills and the ability to explore a computer\\’s software and
hardware without the owner\\’s permission. Their intention can either be to simply gain knowledge or to illegally make
changes.
Which of the following class of hacker refers to an individual who works both offensively and defensively at various
times?
A. White Hat
B. Suicide Hacker
C. Gray Hat
D. Black Hat
Correct Answer: C
QUESTION 10
This wireless security protocol allows 192-bit minimum-strength security protocols and cryptographic tools to protect
sensitive data, such as GCMP-2S6. MMAC-SHA384, and ECDSA using a 384-bit elliptic curve. Which is this wireless
security protocol?
A. WPA2 Personal
B. WPA3-Personal
C. WPA2-Enterprise
D. WPA3-Enterprise
Correct Answer: D
Enterprise, governments, and financial institutions have greater security with WPA3-Enterprise. WPA3Enterprise builds
upon WPA2 and ensures the consistent application of security protocol across the network.WPA3-Enterprise also offers
an optional mode using 192-bit minimum-strength security protocols and cryptographic tools to raised protect sensitive
data:?Authenticated encryption: 256-bit Galois/Counter Mode Protocol (GCMP-256)?Key derivation and confirmation:
384- bit Hashed Message Authentication Mode (HMAC) with Secure Hash Algorithm (HMAC-SHA384)?Key
establishment and authentication: Elliptic Curve Diffie-Hellman (ECDH) exchange and Elliptic Curve Digital Signature
Algorithm (ECDSA) employing a 384-bit elliptic curve?Robust management frame protection: 256-bit
Broadcast/Multicast Integrity Protocol Galois Message Authentication Code (BIP-GMAC-256)The 192-bit security mode
offered by WPA3- Enterprise ensures the proper combination of cryptographic tools are used and sets a uniform
baseline of security within a WPA3 network.
QUESTION 11
Henry Is a cyber security specialist hired by BlackEye – Cyber security solutions. He was tasked with discovering the
operating system (OS) of a host. He used the Unkornscan tool to discover the OS of the target system. As a result, he
obtained a TTL value, which Indicates that the target system is running a Windows OS. Identify the TTL value Henry
obtained, which indicates that the target OS is Windows.
A. 64
B. 128
C. 255
D. 138
Correct Answer: B
QUESTION 12
The establishment of a TCP connection involves a negotiation called three-way handshake. What type of message does
the client send to the server in order to begin this negotiation?
A. ACK
B. SYN
C. RST
D. SYN-ACK
Correct Answer: B
QUESTION 13
An Intrusion Detection System (IDS) has alerted the network administrator to a possibly malicious sequence of packets
sent to a Web server in the network\\’s external DMZ. The packet traffic was captured by the IDS and saved to a PCAP
file. What type of network tool can be used to determine if these packets are genuinely malicious or simply a false
positive?
A. Protocol analyzer
B. Network sniffer
C. Intrusion Prevention System (IPS)
D. Vulnerability scanner
Correct Answer: A
[2021.4 Update] 312-50V11 Exam Questions Answers Free https://www.certificationvce.com/new-free-share-best-online-resource-ec-council-312-50v11-pdf-312-50v11-practice-test/
Pass4itsure EC-COUNCIL dumps discount code 2021 free share
The last sentence:
This blog shares the latest EC-COUNCIL 312-50V11 exam questions, and answers! EC-COUNCIL 312-50V11 pdf, EC-COUNCIL 312-50V11 exam video! Get full Pass4itsure 100% pass & stable EC-COUNCIL 312-50V11 dumps!
ps.
Latest update EC-COUNCIL 312-50V11 exam dumps: https://www.pass4itsure.com/312-50v11.html
[PDF] Free EC-COUNCIL 312-50V11 pdf: https://drive.google.com/file/d/1xZM63lHp46CFESTKrsT8Spj-cJGxC42A/view?usp=sharing